Freelancer.com Stored XSS
On the 8th of August 2013, I reported a persistent cross-site scripting vulnerability on freelancer.com, located in the picture upload function of the website. The bug was fixed on the 27th of August 2013.
Details#
- An attacker creates an image and set its file name to an XSS attack vector. For example,
<img src="" onerror="javascript:alert(1)">.png. - The attacker uploads the image.
- Wherever the image is used, the site will print out the name of the image, which will execute the XSS payload.
Bug Bounty#
Freelancer.com bug bounty program rewards include:
- A freelancer.com t-shirt.
- Listing on freelancer.com's Hall of Fame. – http://www.freelancer.com/info/security-hall-of-fame.php
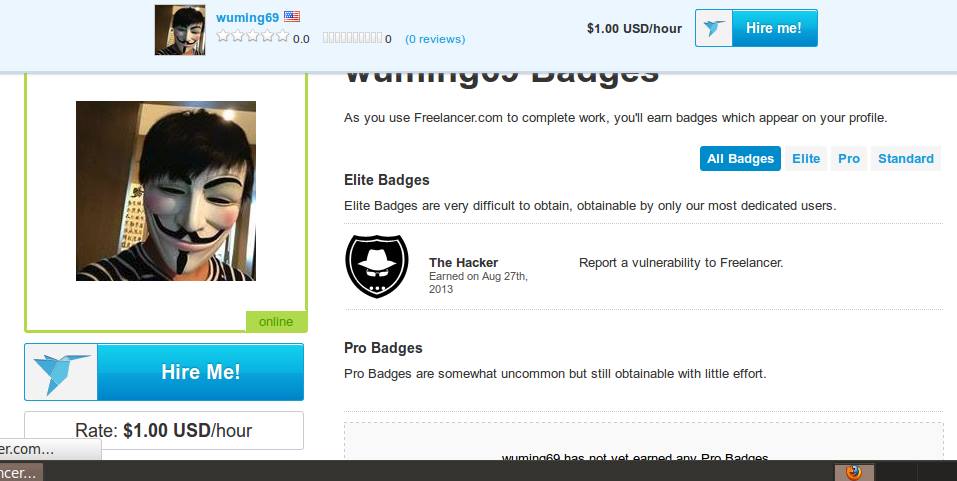
- A whitehat hacker badge for your freelancer’s profile. - http://www.freelancer.com/u/wuming69.html

info
Freelancer.com Alexa Global Rank (at the time): 534.